A Guide to Email authentication Can Protect Your Company and Customers, Says ValiMail’s CEO & Co-founder Alexander García-Tobar
ValiMail’s 2017 Email Fraud Landscape Report revealed that just 0.5 percent of the top million domains have taken steps to protect themselves from impersonation by email authentication.
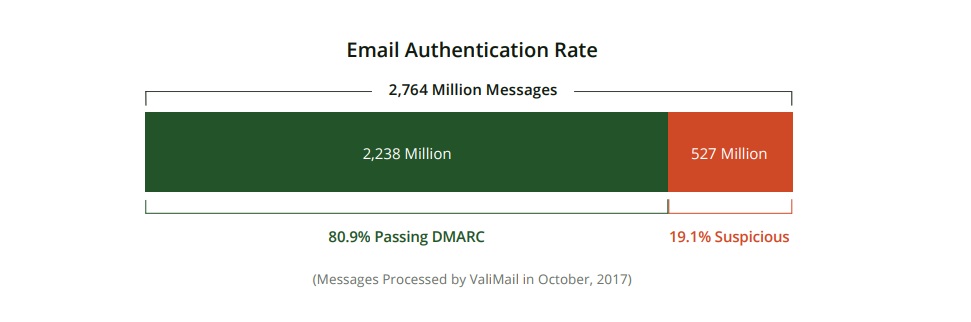
One in five messages sent today is suspicious (i.e. it appears to come from a domain that has not authorized the sender).
There are technical controls, known as email authentication, that can help mitigate the email fraud threat, but only a tiny percentage of domain owners are taking advantage of them. Email authentication refers to a suite of open standards that can stop the most common and hardest-to-detect type of email fraud: Impersonation of people or companies by using their domain names. Without email authentication, fraudsters can easily impersonate any domain simply by putting it into the ‘From’ field of their messages.
For its report, ValiMail examined more than 127,000 DMARC (Domain-based Message Authentication, Reporting & Conformance) aggregate reports for 12 domains (a subset of the domains we process for our customers) during the month of October. Out of more than 2.8 billion email messages processed for this set of domains, 526 million failed DMARC authentications. Of those, they categorized virtually all as suspicious: possibly fraudulent messages from senders not authorized by the domain owners. That means almost 1 out of every 5 emails failed authentication — in other words, was potentially fraudulent.
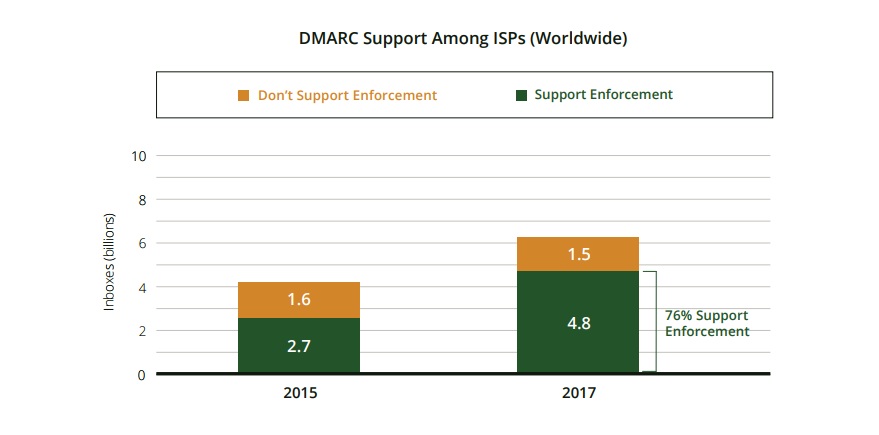
DMARC is a widely used standard that ensures only authorized senders can use an organization’s domain name in their emails. However, the report also found that among the top million domains, 96.4 percent still have not published DMARC records — despite the fact that the overwhelming majority of email inboxes support it. These domains are not using a valuable, accessible tool for protecting themselves against fraud and phishing. This is the DMARC adoption gap.
Furthermore, 77 percent of domains that do publish a DMARC record do not get to enforcement — a rate comparable to what we found when we first analyzed the top million domains in November 2016. They leave their DMARC policies in a monitoring-only mode, and thus fail to actually lock down their email domains to stop impersonation attacks and protect their brands. This is the DMARC enforcement gap.
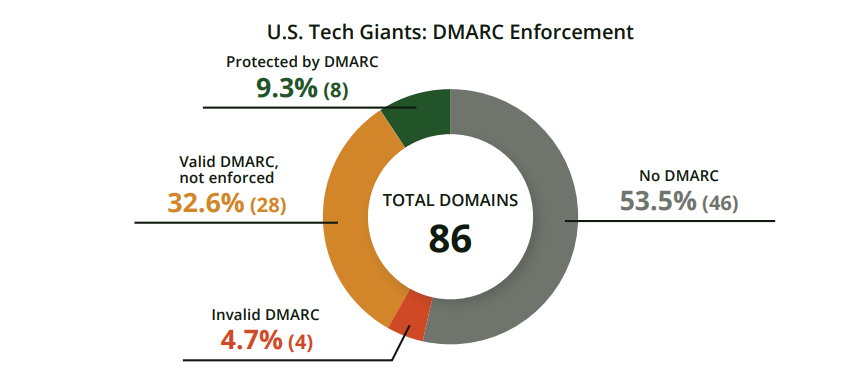
ValiMail’s analysis of the most popular 1 million global domains shows that most domain owners have not attempted to implement fraud protection through the latest and most complete form of protection, DMARC. Of those that have attempted DMARC, only 23 percent are actually achieving protection from fraud.
The report attributes these shortfalls in adoption to the difficulty that domain owners have in fully implementing and maintaining DMARC and its underlying standards (SPF, DKIM), particularly in complex environments where companies use many different cloud-based email services (often without full knowledge of IT staff).

ValiMail’s CEO & Co-founder Alexander García-Tobar talks to MTS about what companies can do to protect themselves from email fraud.
The challenges of implementing the DMARC policy
- Configuration – identification and authentication of 3rd party services
- Difficulty of interpreting DMARC aggregate reports
- Standards limitations/repeated risky DNS changes
- Maintaining authentication ongoing
DMARC is difficult for many companies to implement for a variety of reasons. One is that the underlying standards (SPF and DKIM) were made for an earlier, pre-cloud era. Now that most companies use a dozen or more different cloud services, many of which send email on their behalf, configuring SPF, DKIM, and DMARC to whitelist all these services can be tricky.
Another reason is that DMARC reports can be hard for companies to interpret. These reports are indispensable for feedback, but they are basically XML files with long lists of IP addresses. It can be hard to figure out which IPs correspond to which services.
Finally, email delivery is a high stakes game. Nobody wants to make a DNS change that suddenly stops critical emails from getting delivered. This makes many companies nervous about moving DMARC to enforcement. It gets even trickier as companies’ email partners change: A SaaS provider changes the servers it’s using, for instance, or someone in your company engages a new cloud provider.
Read More: The Best Email Marketing Software According to G2 Crowd Fall 2017 Rankings, Based on User Reviews
How SMBs can tackle the same issue
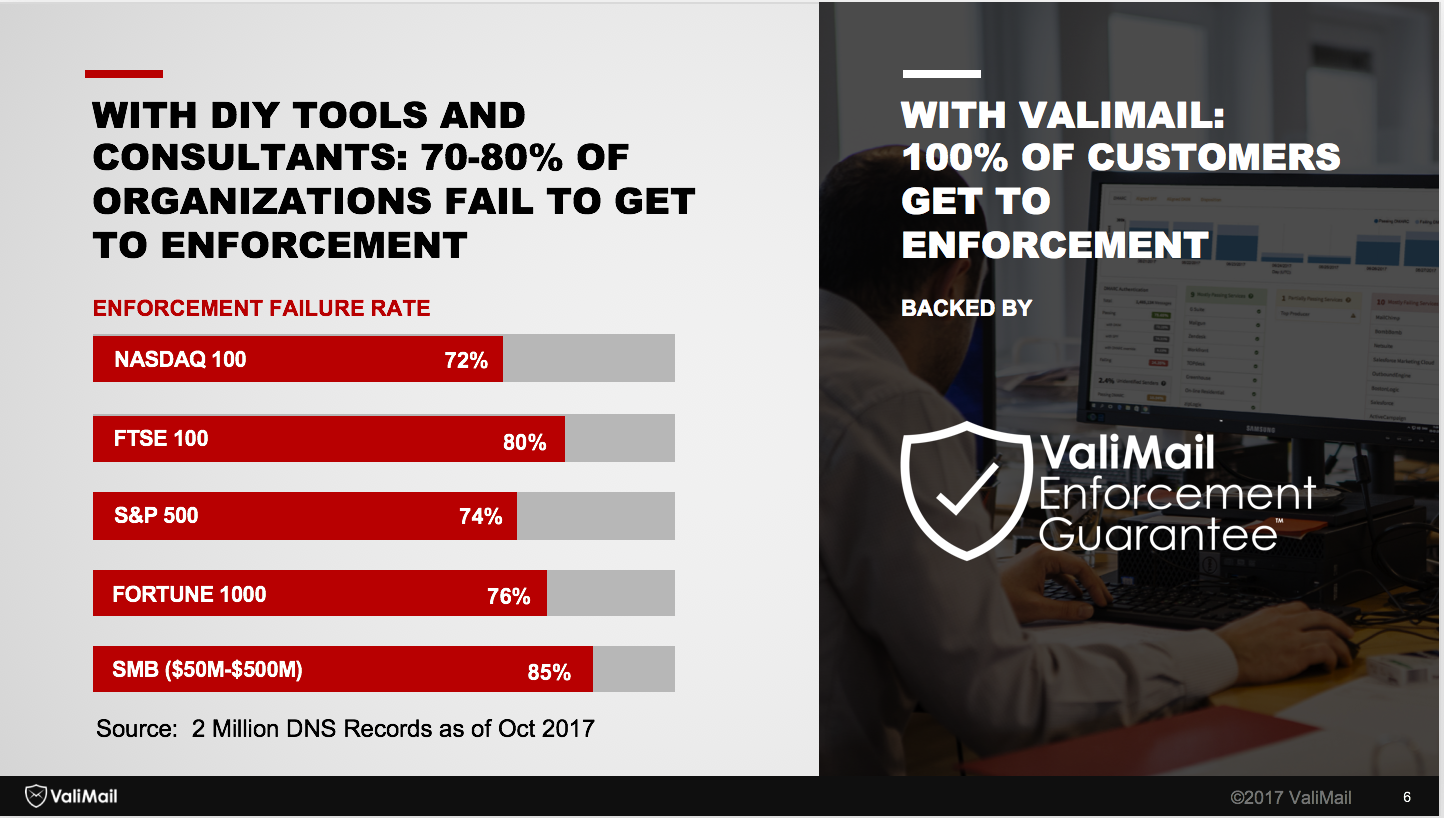
SMBs have less resources but generally simpler ecosystems (fewer email services) while large companies have more resources but more complexity. In the end, these cancel out (see chart below) and 70-80% failure rates are about the same.
When using third party cloud services
The answer is two-fold:
- Internally: lock down your domain via email authentication. With the right implementation, this provides your company with visibility and control over 3rd party solutions. Only authorized vendors will be able to send as you.
- Make sure that the authorization of a 3rd party service includes a security and authentication review. If the vendor fails this, re-consider allowing them to send as you.
Don’t Compromise Brand Safety
- Without email authentication at enforcement (locked down so that messages failing authentication are quarantined to spam folders or deleted), any criminal can send as your brand. This compromises your brand reputation outright. Would a client trust your company if they get a fake email that appears to be from you?
- The use of your domain/brand by a criminal can drastically impact your company’s email sending reputation – lowering your deliverability rates. So your #1 communication method with your clients is now crippled.
- Every time you read that a fake email as company XYZ caused damages you immediately see the impact. Just one example: Coupa was impersonated by a fraudster looking for employee W-2 forms.
One thing to note: This kind of W-2 fraud increased sharply in 2017, according to the IRS.
We know from various research studies that email impersonation is the leading type of phishing attack that leads to account compromise, wire fraud, or W-2 fraud. (Here’s a recent example of this research, from Great Horn.
Impersonation means that the phishing email contains the exact company name and email address, even though the message is coming from a fraudster and contains malicious links or attachments. This makes it very, very difficult for recipients to tell that the message is fake. The advice to “look carefully at the sender” doesn’t apply in this case, because the sender looks completely legitimate.
How ValiMail solutions works towards keeping clients safe
ValiMail was founded to ensure 100% enforcement in a fully automated approach for every company attempting email authentication. The fact that doing it yourself or using the current vendors results in only 20-40% enforcement rates, after 6-12 months of manual work, is not acceptable.
ValiMail automates email authentication with a cloud-based service that guarantees that DMARC and SPF records are always up to date and that each receiving email gateway gets complete, correct information every time.
In short, we manage our clients’ global whitelists as opposed to providing consulting services and forcing the client to manually tweak their DNS. We do this with a patented DNS service that delivers tailored global white lists to each mail gateway that requests it.
We also have the world’s most comprehensive database of email senders, enabling us to turn the inscrutable IP addresses provided by DMARC aggregate reports into actionable information about which senders are using your domain.
Finally, we are the only email authentication vendor to offer a guarantee. We get 100% our customers to enforcement (a DMARC policy of “quarantine” or “reject”), guaranteed.
Recommended Read: ZeroBounce Leads in Encryption Methodology for E-Mail List Protection












Comments are closed.